How to perform Authoritative Restore of Active Directory Objects – 2012 R2
How to perform Authoritative Restore of Active Directory Objects – 2012 R2
In the old post, we learned the steps to perform non-authoritative restore. In this post, we’ll learn the steps to recover deleted OU and users by performing Authoritative restore of System state backup on Windows Server 2012 R2.
Let’s assume a scenario in which we have two Domain Controllers i.e. DC01 and DC02, and we have taken System State backup from first Domain Controller i.e. DC01. After taking System State backup, Administrator has deleted “Sales” OU by mistake and not we have to restore the deleted OU by using Authoritative restore on Windows Server 2012 R2.
Please take a note, non-authoritative restore is the pre-requisite for Authoritative restore. However, in this article, we’ll run all the steps to restore deleted OU and deleted users, including the steps of non-authoritative restore.
1. To restore deleted OU and delete users by using Authoritative restore, open Run and type “msconfig” on first Domain controller. It will help us to boot the server in DSRM mode. As we cannot recover deleted OU or User or perform authoritative restore while DC is running, we have to boot the server in DSRM mode for a recovery process.

2. On System Configuration console, on Boot tab, under Safe boot options select “Active Directory Repair” and click on apply and Ok. It will boot the server in DSRM mode. Alternatively, we can manually boot the server in DSRM mode by pressing F8 repeatedly after the BIOS screen. Select the option of Directory Service Repair mode from the Advanced Boot Options and click enter.

3. In DSRM mode, open Windows Server Backup and click on “Recover” for starting the recovery process.

4. On Getting Started console, select “This Server” if the backup is stored on the same server or select “A backup stored on another location” if the backup is stored on some other location. Click on Next to continue.

5. On Select Backup Date console, select the date and time of the backup which we have to restore. Click on Next.

6. On Select Recovery Type console, select the option which we want to recover. Here, we will continue with the option of “System State” as we have to restore the Active Directory object. Click on Next to proceed.

7. On Select Location for System State Recovery console, select the option of “Original Location” and click on Next.

8. On Confirmation console, verify the items to be recovered and click on “Recover“.

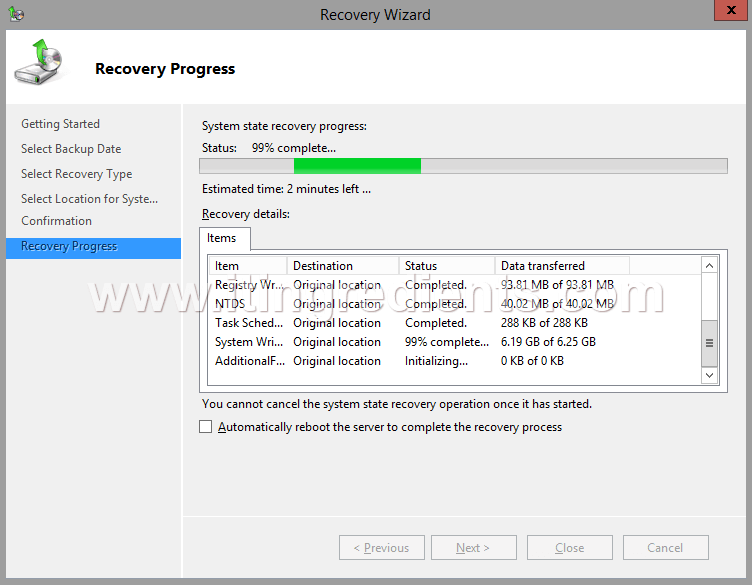
9. On Recovery Progress console, we can see the recovery progress. Click on close to close the console when the recovery is completed and don’t restart the Server.
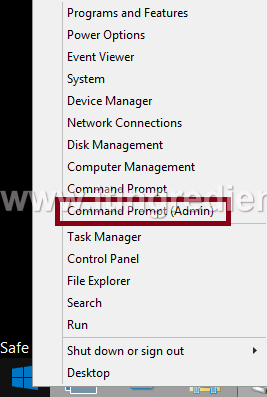
10. Before restarting the server, open Command Prompt to complete the steps to perform Authoritative Restore.
11. On Command Prompt, type “ntdsutil” and hit enter. It will give us access to manage Active Directory database.
Now type “activate instance ntds” and press enter.
Then type “authoritative restore” and hit enter. Type “restore subtree ou=Sales,dc=itingredients,dc=com” and press enter. In this command, Sales is a name of the deleted OU which we want to restore by using the process of authoritative restore and itingredients.com is the name of our domain.

12. A dialog box appears regarding the confirmation of performing Authoritative Restore. Click on Yes.

13. After the successful completion of Authoritative Restore, before restarting the server again run “msconfig” and uncheck the safe boot option, this is to revert the changes that we performed during step 1 and 2. Now, restart the server.
Note: Read the summary after you see the message “Authoritative Restore completed successfully”. It shows the details of all the records that are restored. In this example, we can see the message “Successfully updated 11 records”.

14. Once the Domain Controller is rebooted in normal mode. Open Active Directory Users and Computers, and verify that the deleted OU and all its deleted users are restored successfully.

Note: Non-Authoritative restore is the pre-requisite for Authoritative restore. In the future article, we’ll learn the steps of restoring deleted users using the Active Directory recycle bin.

